must not be placed where they may be used by intruders to gain entry. Alarm signs must not create nuisance
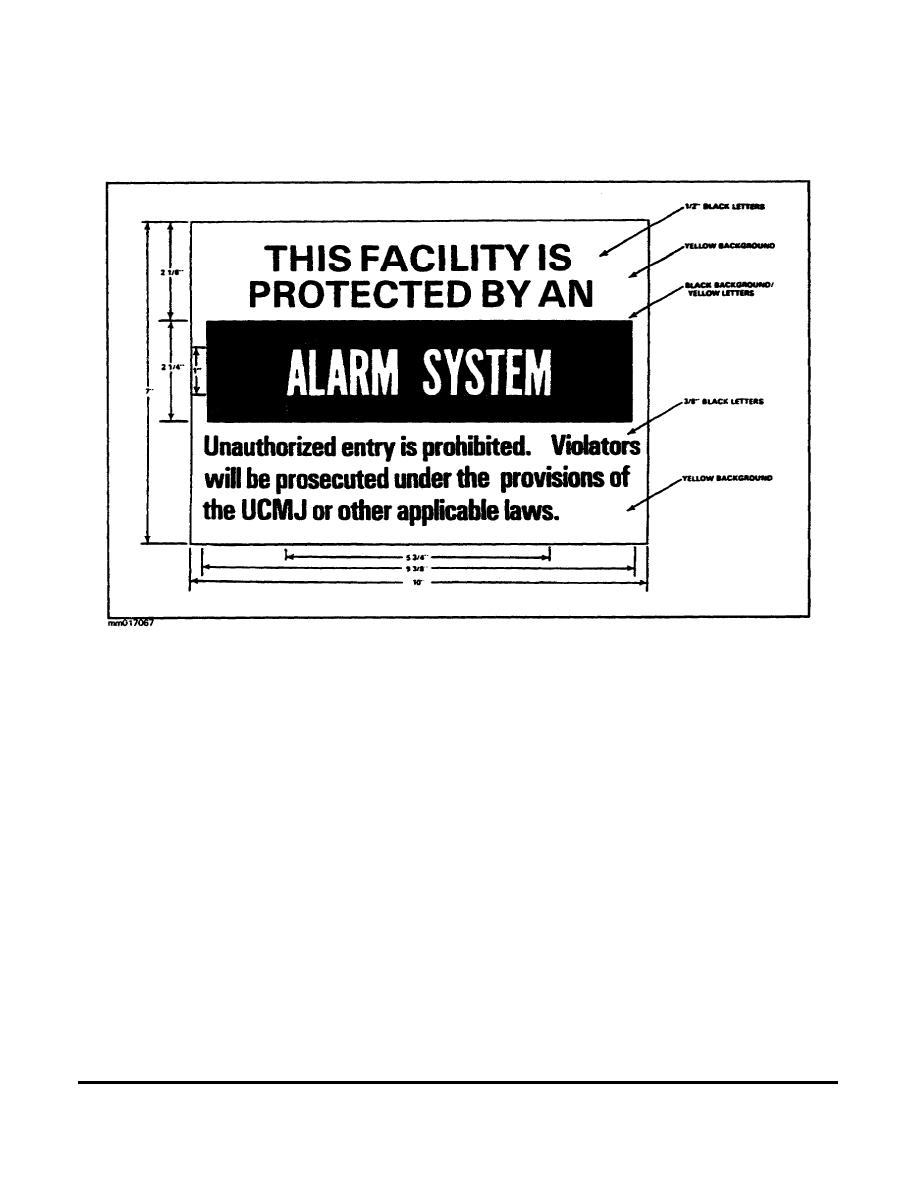
alarms. If they do, they must be posted outside the perimeter fence. IDS signs such as the one depicted in Figure
3-4 must be used.
Figure 3-4. Sample intrusion detection system sign.
Computer Security
Computers are expensive, and they control a great deal of important information. Damage to a computer can
result in costly repairs and the loss of critical information. Therefore, computers present special security
problems involving the physical computer, the user, the hacker, and the computer media. Terminals connected to
a mainframe require the same procedural and physical protection as the mainframe itself. All components must
be protected.
The degree of protection a computer system needs is determined by what kind of information is stored in it. A
system containing Top Secret data needs more protection than one used for unclassified data. Because there are
many ways to provide security, several protective measures may be used in combination. It is unusual for one
measure to be used alone. The paragraphs that follow describe some security measures that can be employed to
protect computer systems.
Indoctrination and Training. These must be initiated as soon as personnel come on board. An annual
refresher that is tailored to the duties should also be conducted. The training should include individual
responsibilities, threats to the system, vulnerabilities; and countermeasures. SOPs can be used to familiarize
everyone on the staff with what is normal. This can aid in spotting actions that are out of the ordinary.
3-17
MM0170




 Previous Page
Previous Page
